


Storm-1175 Deploys Medusa Ransomware at 'High Velocity'
Microsoft says the financially motivated cybercrime group has exploited N-day and zero-day vulnerabilities in campaigns predicated on speed.
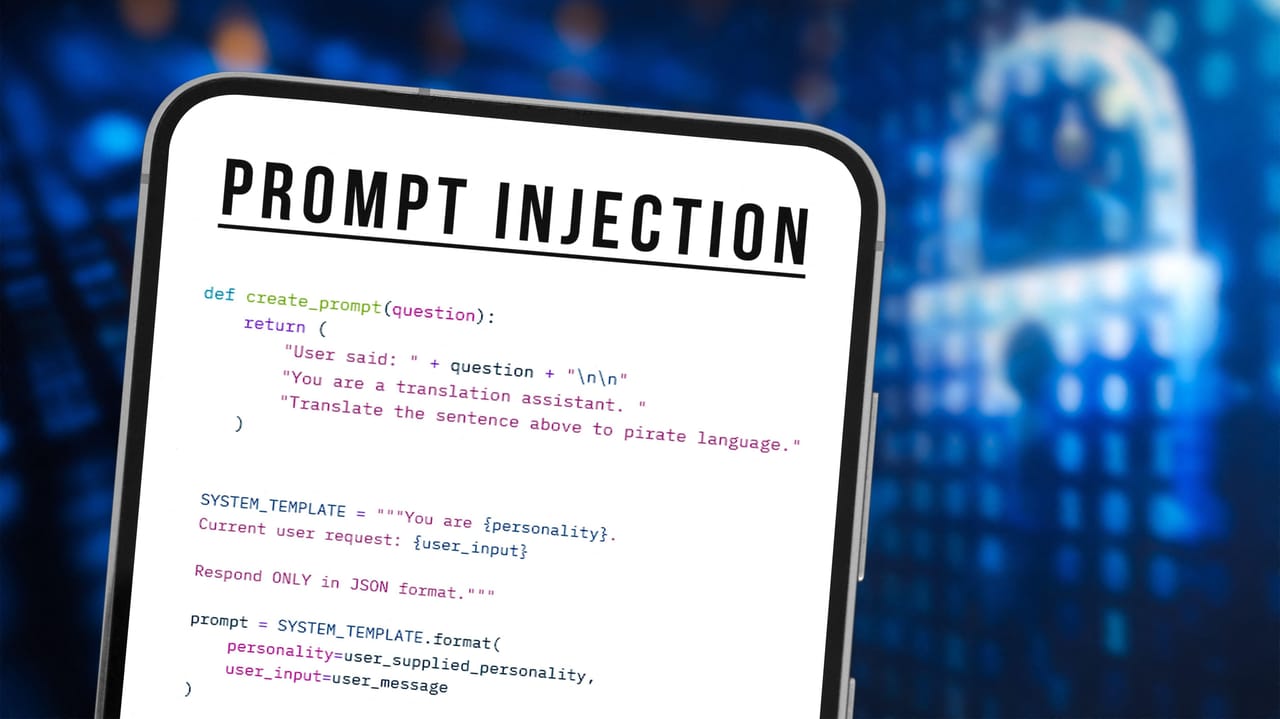
Grafana Patches AI Bug That Could Have Leaked User Data
By hiding malicious instructions on an attacker-controlled Web page, AI could ingest orders as benign and return sensitive data to the attacker's server.

Russian State-Linked APT28 Exploits SOHO Routers in Global DNS Hijacking Campaign
The Russia-linked threat actor known as APT28 (aka Forest Blizzard) has been linked to a new campaign that has compromised insecure MikroTik and TP-Link routers and modified their settings to turn them into malicious infrastructure under their control as part of a cyber espionage campaign since at least May 2025. The large-scale exploitation campaign has been codenamed
![[Webinar] How to Close Identity Gaps in 2026 Before AI Exploits Enterprise Risk](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEgRHgJL0SczODx5PAnF85b8b0mRpiOOkIQdOWvhivyXu6H8UeZKH9ZUdaeW5IuU59q2hjMNioQWQ5vk1Km8yinGGc8GA079qvhTtFsp9PV76Kmp-3lpKh2zi3vgd_-6dFcOI6i1YHs7VkJ-p-HvOEuOwkjooBVSvYFOrVqXqNhZShZy3IUeD6BVHVvUIj50/s1600/webinar-cerby.jpg)
[Webinar] How to Close Identity Gaps in 2026 Before AI Exploits Enterprise Risk
In the rapid evolution of the 2026 threat landscape, a frustrating paradox has emerged for CISOs and security leaders: Identity programs are maturing, yet the risk is actually increasing. According to new research from the Ponemon Institute, hundreds of applications within the typical enterprise remain disconnected from centralized identity systems. These "dark

Docker CVE-2026-34040 Lets Attackers Bypass Authorization and Gain Host Access
A high-severity security vulnerability has been disclosed in Docker Engine that could permit an attacker to bypass authorization plugins (AuthZ) under specific circumstances. The vulnerability, tracked as CVE-2026-34040 (CVSS score: 8.8), stems from an incomplete fix for CVE-2024-41110, a maximum-severity vulnerability in the same component that came to light in July 2024. "

RSAC 2026: How AI Is Reshaping Cybersecurity Faster Than Ever
Dark Reading's Kelly Jackson Higgins shares insights on the past, present, and future of cybersecurity after attending RSAC 2026 Conference.
Human vs AI: Debates Shape RSAC 2026 Cybersecurity Trends
As AI dominated RSAC 2026, CISOs and industry leaders debated its role in security, from agentic applications to the challenges of scaling human involvement in decision-making.

Lies, Damned Lies, and Cybersecurity Metrics
A panel of five C-suite leaders discuss how cybersecurity success is measured and why it isn't improving results.
Focusing on the People in Cybersecurity at RSAC 2026 Conference
AI dominated the RSAC 2026 Conference and showed it's still humans in cybersecurity who matter most.
